The National Security Agency (NSA), Cybersecurity and Infrastructure Security Agency (CISA), and National Institute of Standards and Technology (NIST) warned that cyber actors could target our nation’s most sensitive information now and leverage future quantum computing technology to break traditional non-quantum-resistant cryptographic algorithms. This could be particularly devastating to sensitive information with long-term secrecy requirements.
The joint Cybersecurity Information Sheet (CSI), “Quantum-Readiness: Migration to Post-Quantum Cryptography,” helps the Department of Defense, National Security System (NSS) owners, the Defense Industrial Base (DIB), and others proactively protect the confidentiality, integrity, and authenticity of sensitive information.
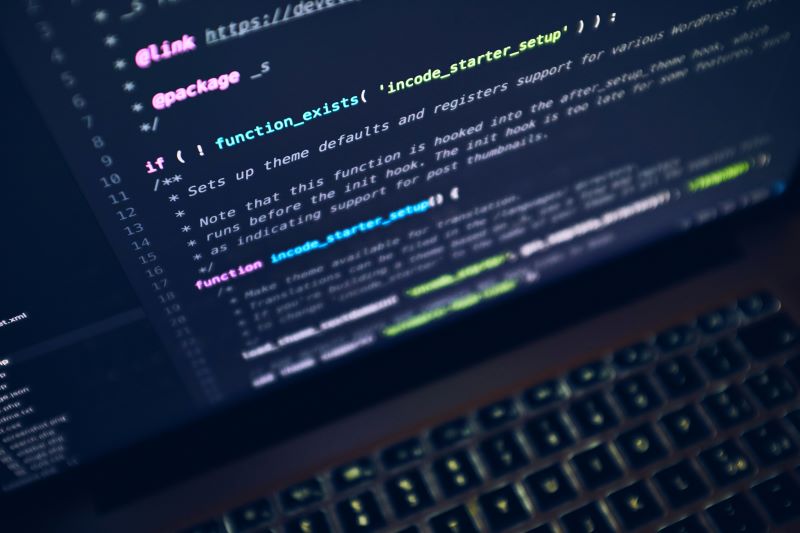
“Post-quantum cryptography is about proactively developing and building capabilities to secure critical information and systems from being compromised through the use of quantum computers,” said Rob Joyce, Director of NSA Cybersecurity. “The transition to a secured quantum computing era is a long-term intensive community effort that will require extensive collaboration between government and industry. The key is to be on this journey today and not wait until the last minute.”
The report contains recommendations for organizations to develop a quantum-readiness roadmap and prepare for future implementation of the post-quantum cryptographic (PQC) standards, which NIST expects to publish in 2024, including steps to effectively prioritize migration efforts. Taking these measures will increase an organization’s security posture against potential malicious use of quantum computers.
CISA, NIST, and NSA urge organizations to start preparing for the implementation of post-quantum cryptography by doing the following:
- Establish a Quantum-Readiness Roadmap.
- Engage with technology vendors to discuss post-quantum roadmaps.
- Conduct an inventory to identify and understand cryptographic systems and assets.
- Create migration plans that prioritize the most sensitive and critical assets.
By implementing the steps detailed in this CSI, organizations can effectively assess their reliance on cryptographic systems and assets, and prioritize their migration efforts to ensure compatibility with the upcoming PQC standards and meet the goals and timelines in National Security Memorandum (NSM) 10.
Source: NSA
Like IC News? Then please consider subscribing. You’ll get full access to our searchable library of 10,000+ articles, plus new articles each weekday.